Blog
News, tips, and resources by and for the nonprofit technology community.Choosing a mobile messaging vendor shouldn’t be this hard
May 11, 2026
6 minute read
Meghan McLaughlin
BRAC USA
Why nonprofits are missing from the responsible disclosure ecosystem
Apr 23, 2026
7 minute read
Jared Medeiros
Harbor Project
Innovative phishing simulations to build cyber-resilience
Apr 7, 2026
7 minute read
Atish Kumar Dash
Advance Solutions Corp.
Technology adoption in nonprofits: An analysis of NTEN’s Tech Accelerate data
Jan 5, 2026
5 minute read
Jason Samuels
W4Sight, LLC
Keep your website traffic up in an AI-first search world
Aug 28, 2025
11 minute read
Rosie Gladden
ImageX
Meet rising compliance requirements with smarter workflows
Aug 20, 2025
5 minute read
Matt Tengtrakool
Givefront
Seven ways to build an equitable website
Jun 16, 2025
7 minute read
Laura S. Quinn
Laura S. Quinn Consulting
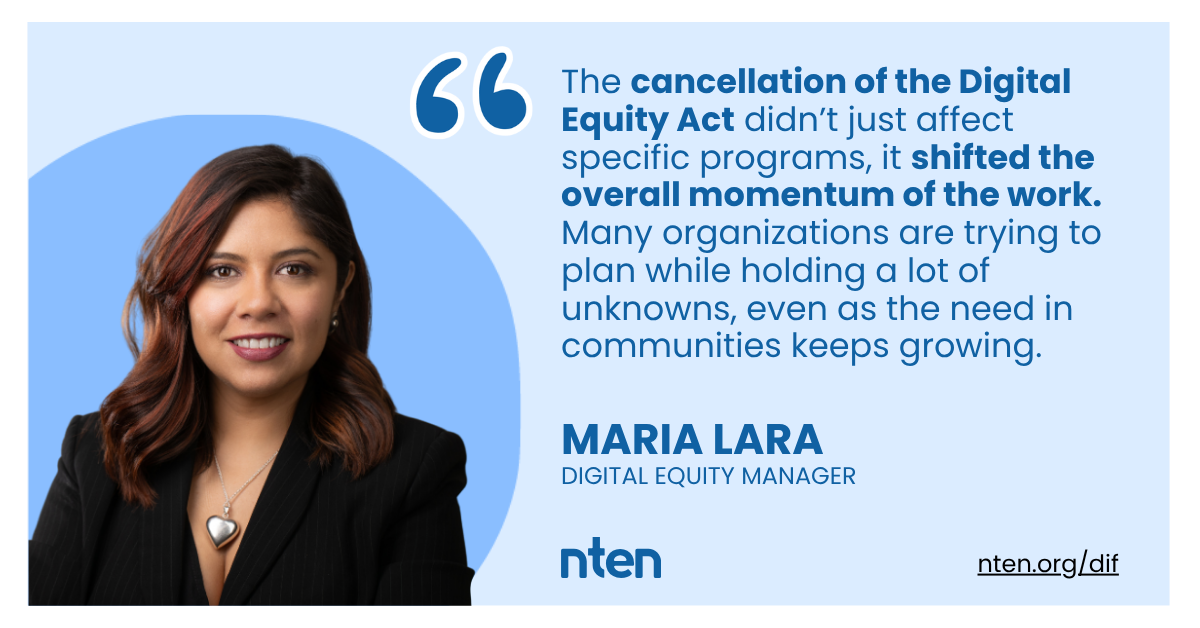
Digital equity is a key enabler to public participation and stronger communities
May 10, 2025
4 minute read
Write for NTEN
We're always looking for articles from our members and the broader nonprofit tech community.
Learn more